This involves assessing the overall security posture of the IT infrastructure. An effective network infrastructure audit process will identify existing vulnerabilities and gaps in policy implementation. This usually evaluating both the hardware and software with the aim of enhancing the security posture of the organization. As a matter of fact, these audits normally will help companies in mitigating risk and maintaining overall data integrity. ORACO Kenya is your partner for cyber threat protection and IT infrastructure audit provider.

IT infrastructure audit inventory
Here we identify all the ICT assets; both physical and virtual deployments. We create a new asset register or build on the existing asset register. The asset inventory will capture both hardware and software assets. The hardware include VoIP PBX, desk phones, the firewall, router, computers, printers, servers, wireless access points, network switches etc.
Be that as it may, a lot of security breaches actually happens through the physical assets. To avoid unauthorized access, physical security can play an important role. For instance, installation of biometric access control systems can address the issue of unauthorized access.
Unauthorized access can also be implemented at the software level. Here, we create user access logins and advice users to regularly update passwords. the software includes Windows operating system, Word processing applications, endpoint and server security software.
Performance analysis
This involves evaluating traffic and network bandwidth utilization. Performance analysis uncovers how fast users can access the hosted services through the local area network. Here, we focus on server performance, and internet speeds. Also check how effectively the network infrastructure support cloud applications and remote working.
see; biometric clock in system
Software security assessment
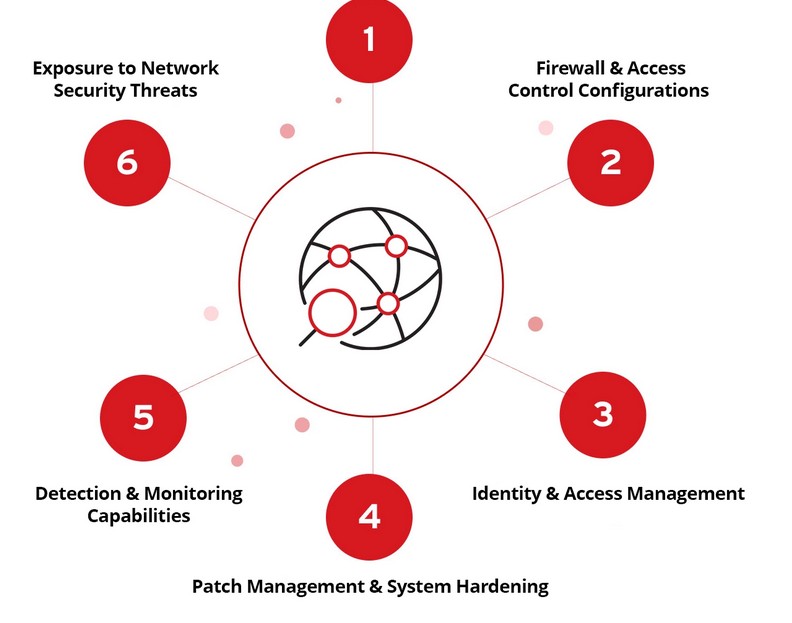
Security assessments involves scanning vulnerabilities existing in endpoints and the active network devices. We check adherence to regular firmware updates, patch management and software updates.
Security assessment will also network firewall and Endpoint security and protection solution. We analyze the capability of the antivirus solution in preventing and stopping malware attacks. Also, we review network firewall capability to handle intrusion prevention and protection against cyber-attack threats.
Security assessment also involves looking at password management policy. Password expiry and give advice on strong password policy. For instance, the use of multi factor authentication system can be boost the overall IT infrastructure security posture. We also review existing user privileges. Access levels for critical infrastructure services. Super admin user rights, ordinary user access levels, checks and balances for users with super user privileges.

Wireless network security
To begin with, all the rogue wireless access points should be blocked. Even so, there should be separate SSIDs to separate corporate Wi-Fi users from the guest users. Ordinarily, guest Wi-Fi users have limited access to network resources. There should be expiring sessions for guest Wi-Fi users. At the point of installation, secure encryption protocols to be implemented to enhance Wi-Fi network security.
Physical security audit
Physical security infrastructure includes the CCTV cameras installation, intruder alarm system and the biometric access control systems. As a standard, the combination of CCTV surveillance and biometric access control systems should be deployed for IT server room. Likewise, general office security requires installation of CCTV surveillance in common work spaces. And the biometric access control can be installed to man the main office door.
see; walk through metal detector price
User permission must be reviewed to prevent situations where user gain unauthorized access to company resources. In fact, former employee access credentials should be disabled. Access control logs should be safe and secure and accessible when need be. Likewise, CCTV camera recordings should be safe and allow for playbacks in the event of a physical security breach. In as much as surveillance hard disks have automatic overwrite, the most recent footage should cover as long as one month.
Configurations review
The focus here revolves around reviewing active network devices as part of the IT infrastructure audit exercise. These include network firewall, managed network switches, wireless access points and endpoint security protection software. We analyze firewall rules. Gateway level traffic analysis. Firewall configurations must ensure proper traffic filtering.
see; pedestrian turnstile gate
Email security. We also look at email security and anti-spam protection rules. Malware attacks and computer virus can be distributed through unsolicited emails. Besides proper email security configurations, user training can be protect against social engineering attacks. Proper configurations will help protecting data against breaches. Also, once vulnerabilities have been identified, steps must be taken to patch identified weak points.



