Eset endpoint antivirus has enhanced the integrity of data stored in communication devices such as servers, and end-user computers. Personal data, as well as official company information, are at the risk of manipulation. Thus IT Support Companies, as well as Eset endpoint antivirus distributors in Kenya, offer various products for ensuring computer security. Even smartphones, PDAs and tablets have not been left behind either. This is due to risks posed by malware and phishing programs targeting internet users.
see; best payroll software for large companies in Kenya
On the bright side though, there are so many antivirus programs out there. As ORACO Kenya, we are proud to be one of the few Eset endpoint multi device protection license for business in Kenya.

We know that choosing the best antivirus program can be a difficult exercise. We have come up with a guide to help you select the best antivirus software. And below are the critical features to look for in the best antivirus software:
see; PBX telephone system
Eset Endpoint Antivirus installation
The best antivirus software is obviously one that does not require a lot of system memory to run. Higher usage of system memory usually results in the slowing down of the computer operation. This can be seen in the time taken to open a word document or launch the browser. We know that users worry so much about their computer slowing down when the antivirus program is running in the background. That is why low memory programs are preferable to heavy ones. And the best antivirus software does not require a high specification computer.
Internet and Web Security
Most endpoint security software usually provides protection against virus attacks through USB ports. The more advanced software provides protection from attacks during internet browsing sessions. Good endpoint security software should warn users against malicious online content. It should also block internet users from accessing infected websites. Security software, especially internet security programs, usually filter out suspect results from the search engine. This presents you with a secure browsing experience.
Remote device management
Eset endpoint antivirus software offers a proactive approach to device protection. Research shows that a lot of viruses are transferred into computers via USB ports. The endpoint protection system should automatically scan and cleanse the USB storage without user prompt. This kind of proactive approach is an important feature for any endpoint protection software. In fact, the very effective anti-malware software provide round the clock protection.
see; VoIP trunk provider
Technological innovation in the Information technology industry presents complex challenges for IT security professionals. The focus of yesteryear was on endpoint protection and server security. Today, the IT security focus areas encompass cloud security, ransomware attacks, and mobile security. Also, internet background radiation whereupon remote desktop protocol applications get exploited by attackers. Also protection for the cloud PBX.
see; structured cabling installation
And the age of bringing your own device (BYOD) further complicates people and information systems security. This is because, with a weak BYOD policy, smartphones will only be protected while being used within the corporate network environment. And become vulnerable to attackers when outside the office because of the unsecured wireless network.
Today, the attackers keep perfecting ways of evading detection even as attacks are being executed. And the trend is fast moving towards the use of automated tools to execute evasive attacks.
By way of example, services and applications that can access the internet tend to be the main areas for system vulnerability. The same applications and services provide the main entry point to file servers, wireless networks, backup storage, and IP PBX phone system. A better understanding of the security environment will lead to better decisions made by the clients supported. Ultimately, the best approach would lead to adequate protection of the systems deployed and the people working the system.
The main IT Security focus areas
Remote Desktop Protocol
In as much as remote desktop protocol (RDP) has simplified IT support services for many organizations, it presents a weak point in threat management. Lately, there are a number of tools that support remote and off-site support. Some of these apparently helpful applications have been abused to cause havoc. In most cases, hackers will use brute force when identifying weak RDP-based hosted services.
With a successful login to the network, attackers will use Mimikatz to expose credentials for the superuser. Then, use the super credentials to propagate attacks across the entire network of computers. The end result of such a violation can be devastating. Thus, it is important for network security administrators to be careful exposing local RDP services and applications to the internet.
Ransomware attacks
No doubt, the number of ransomware attack victims keeps increasing. This is because most ransomware attackers are good at escaping detection. And having gained a successful entry into the computer, they use algorithms to encrypt entire storage drives. Therefore, the cyber-attack victim will have to part with some money in order to regain access to the encrypted files.
Why are ransomware attackers successful at their missions? Because they have a better understanding of how ordinary network security firewalls work. Also, they know the capability of a standard endpoint security software. In short, they have mastered the attack landscape. As it is, the solution lies in the implementation of a security solution that offers zero-day threat neutralization, even as a Sophos firewall.
Mobile Security
Today, we have smartphones with processing capability matching that of computers. Furthermore, the amount of sensitive and important information held by these gadgets is amazing. In fact, most job-related transactions can be executed using a smartphone. Hence, attackers have developed mobile malware targeting smartphone owners.
The attacks targeted on smartphones usually come in the form of malicious software installations. In the past, android phone users were the main victims of malicious software. Be that as it may, over time Google has put in place measures curbing downloads of suspicious applications. Still, caution needs to be taken when downloading and installing applications.
SEE: intercom system
Cloud Security
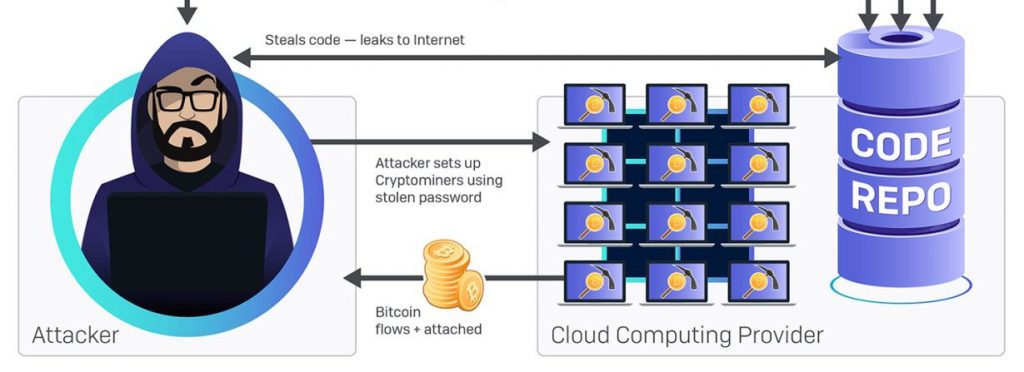
More and more organizations continue migrating core services to the cloud. Hosting services in virtual servers tend to increase efficiency as well as flexibility. In short, the cloud service has provided companies with a platform for running operations efficiently and more profitably. However, the attackers have read the trend and are presently developing malicious codes targeted at cloud services.
see; best call center software
Even though most advanced unified threat management solutions focus on server and endpoint security, still a lot needs to be done about cloud security. Therefore IT security practitioners have an obligation of ensuring that the security solution deployed offers protection for cloud servers.
see; IVR system
Organizations need to recognize that the cybersecurity landscape has greatly shifted over the years. The IT security focus areas we have highlighted above will provide a roadmap for the deployment of cybersecurity tools. Getting the focus right will lead to adequate protection of company data, the devices being used, and the people participating in day-by-day business operations.
Simple to deploy Eset Endpoint Antivirus Security
The best endpoint protection software should be easy to install and simple to interact with. The administration dashboard should also be easy to understand. A simple user interface enhances the overall usability and functional capability. The antivirus will serve no purpose if the IT support technician cannot activate critical protection features.
see; best CCTV installation company
Multi-platform Compatibility
Initially, people thought that only the Windows operating system could be attacked by viruses. Today, Android and even Mac OS face the same challenges. Therefore, it is advisable to purchase an endpoint protection software program that can work across all OS platforms. For maximum protection, it is advisable to install the endpoint security software in the personal computer as well as the Smartphone.
Proactive file scanning
The best endpoint protection software scans all files whether email attachments or downloads from the internet. Apart from documents, audio and video content also contribute to the distribution of malware. Symantec virus removal tool permanently delete affected files. The other programs clean and repair any damaged document. The best action for an infected file should be healing as opposed to permanently deleting. That is, helping the user recover files instead of losing.
see; automatic gate opener system
Finally, remember to buy and install only genuine software. This applies to the operating system as well as other applications. If your system is using a fake operating system then installing genuine antivirus software will not be useful. It is possible to save some money by using unlicensed software. But the truth of the matter is you are creating black holes to be exploited by hackers.
If you have a tight budget for software, you can reach us through this webpage. ORACO Kenya has some exciting discounts on network firewall software. Get full year protection for as low as $10!
The above information will help you in choosing between competing Eset endpoint security protection in Kenya. The features highlighted above will guide you in getting the best endpoint protection software deal. Should you face any challenges, feel free to Contact Us network security and endpoint protection.