Fortinet Firewall in Kenya
Looking for the best firewall for corporate networks? Contact us today for the best Fortinet business firewall in Kenya. ORACO Kenya is a distributor and partner of Fortigate firewall in Kenya. IT systems security has become a very critical area for most organizations. What with cybersecurity threats, malware attacks and escalated virus attacks. Thus, the IT staff would definitely want to upgrade company network security systems. However, it can be a challenge to purchase the right network firewall with the capability to meet organizational IT security challenges. This network firewall buying guide will assist the IT staff in acquiring the best firewall security solution.
Be that as it may, most organizations would like to invest in a computer security system that offers visibility into web and application activity as priority number one. The ability to identify the affected computers, programs, or processes is at the center of timely incident response. Following accurate identification and isolation, cleaning should be fast-tracked to avoid prolonged system downtime.
Best Fortinet business firewall features and specs
- Application identification and control
- Advanced threat protection (ATP)
- Targeted threat performance protection
- Advanced intrusion prevention system (IPS)
- Artificial intelligence and machine learning that boosts pattern recognition
- Coordinated and automated real time protection
- Protection against Distributed Denial of Service (DDoS) Attack
- Advance IPSec VPN performance
See also: best payroll management system
Next, the system should be able to protect the network from threats; not only known but also unknown threats. No organization would risk the loss of data due to a cyber-security attack. Network visibility should help stop infections from spreading, and quicken recovery. Lastly, the solution should offer automated threat detection, isolation, and removal. The firewall depends on different technologies such as exploit detection and deep learning to catch elusive malware. The goal for integrated protection should about achieving maximum benefit from server security, endpoint protection, and the firewall.
Requirements when buying the network firewall
The Intrusion prevention system
Hackers keep upgrading their skills to escape detection during an attack. Therefore, the intrusion prevention technology built into the firewall system should be complex enough to detect attempted breaches. Detecting modern-day malware attacks will require a more sophisticated approach. Because signature-based detecting just cannot cut it. Thus, as this network firewall buying guide recommends a firewall that relies on behavioral analysis technology together with deep learning.
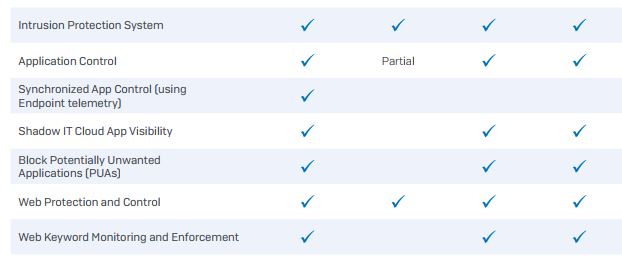
Web security technology
Adequate protection requires the firewall system can detect unwanted apps, bots, and malicious traffic. Above all, web security can only be assured when a system exists to scan DNS addresses and dynamic IPs. Specifically, Web and application firewall technology will be very important for those organizations hosting private servers in-house. The system comes with a reverse proxy to harden the server from being attacked.
see; VoIP trunk provider
The best web security firewall should offer protection against common threats like Cryptojacking. As a matter of fact, most firewalls have inbuilt antivirus engines that continuously emulate JavaScript code on browsers. Still, there should be an efficient synchronization between the firewall and the hosts within a network. Efficient synchronization should reveal the health statuses for every endpoint on the network so that timely action can be taken in case one is compromised.
see; structured cabling installation company
Email security (Antispam)
Most social engineering attacks can be propagated through email. Attackers will likely exploit emails to gain unauthorized entry into a network. Therefore, a good firewall should have a good anti-spam system to protect against network spamming. Also, the firewall should have good anti-phishing technology to protect against password theft and loss of private information. The firewall should automatically subject all incoming emails to thorough scanning including all email attachments.

The capability for multi-site connectivity
Most organizations would like to have multiple secure connections to different locations. Furthermore, VPNs provide secure tunnels for sharing IT infrastructure resources with branch and remote offices. The network firewall should be able to offer a simple yet reliable remote site VPN connection solution. As a matter of fact, most firewalls with advanced features have software-defined wide-area networking for delivering remote site connectivity.
Faster firewall installation and deployment
With a similarity to the IP PBX phone system, network security firewalls come with different deployment options. To begin with, the firewall system can be purchased as a physical appliance. As a physical appliance, it has to be mounted in a network cabinet inside the server room. Mostly, companies would have in place a physical server room access control.
Secondly, the firewall solution can be implemented as a cloud solution. In this case, there will be no purchase of a physical appliance. All the tools required for network security will still be available as in the hardware form. However, the IT security staff will be able to log in to the firewall through the online cloud account.
Advanced firewall performance
Performance remains a key factor when planning to purchase a firewall. The ease with which users can execute various official company tasks will depend on how fast the firewall delivers various services. In particular, cloud services entirely depend on firewall performance. Hence, the IT staff should consider firewall throughput that can not only support the current users but has an allowance to accommodate more people in the future. Additionally, load balancing will also boost WAN performance.
see; Fortigate firewall
Essential firewall services
Automated response and alert
Network visibility is a feature whose value cannot be underrated. In addition to the rich reporting dashboard, the application visibility offer remains an important tool for gathering actionable intelligence. In fact, the firewall should detect and isolate and clean any threats without needing human intervention. And, the logs stored detailing all the actions executed; with an option for rollback. At the bare minimum, these features must be present on any firewall. Fortinet business firewall is designed to offer coordinated and automated real time network protection.
Integrated protection framework
In as much as firewall offer protection at the gateway level, it should not be able to integrate with endpoint security. Such integration will bring about greater coordinated network protection leading to better identification and isolation of threats. With the improved synchronization between the firewall system and the endpoint protection software, it will be easy to control apps and web activity.
Friendly user interface
Sometimes, firewall installation and configurations can be a very frustrating experience. The very first generation of network firewalls proved to be complex to install. Moreover, firewall installation required an elaborate training session from the vendors. With such complexities, clients could not enjoy all the features built into the firewall system.
see; biometric time attendance system
However, the firewall solutions of today have easy to understand interface. Most network protection features can easily be enabled and disabled as need be. The simple user interface has enabled user clients to enjoy the full potential of the firewall. Simplicity in configurations, installations, and deployment remains a key factor in the network firewall buying guide.
The above network firewall buying guide illustrates the key features that must be available in a good firewall for adequate protection. Contact us today for the best network firewall security solution for small, medium, and large enterprises in Kenya.
Firewall can protect from all these cyber attacks
Phishing attack
In this kind of attack, cyber criminal will send an email which appears to be coming from a genuine institution. However, when looked at keenly, the email in fact does not come from a legitimate source. The phishing email normally comes with attachment which when downloaded can install a malware into the local computer. A phishing email might be in the form of a voucher from a supermarket.

Denial of service attack
This kind of attack is propagated when the attackers jam a particular IT service making it unavailable to the authorized users. Denial of service attack would normally target web servers and ERPs. The use of VPN and HTTPS protocols will help protect servers from denial of service attacks.
Inside attack
As the name suggests, an inside attack happens when a former employee gains unauthorized access to company’s IT resources through social engineering. It can also refer to sabotage by a current employee of the company. Fortinet business firewall have been capability to to detect and prevent volumetric inside attack and distributed denial of service attack.
Password attack.
Password attack is sometimes known as brute force attack. Here, bots are used to force login into a legitimate account. The attack will be carried out particularly using an automated software which will use various combinations to generate a password for login. Thus, users are advised not to use the same password for applications. Separating passwords for work related systems and personal applications will likely reduce the impact of a password attack.
SQL injection attack
This is an attacks especially directed at web based applications. During the SQL injection attack, the attackers inserts a malicious code into the main database. The malicious code will then be used to achieve various purposes such as gathering sensitive data about company transactions.
Man in the middle attack
In this kind of attack, an attacker will intercept communication between two parties with the aim of having access to sensitive information being shared on a platform. This type of attack usually target telephony infrastructure such as VoIP PBX where an attacker eavesdrops on a call.
see; Grandstream PBX
Malware attack
This type of attacks is the most common computer attack. Malware attack normally get propagated through USB drives, flash memory drives etc. after being installed in a local computer, it can easily be replicated across the corporate network.
Organizations should use firewall to protect local area network from untrusted traffic. The firewall has the inbuilt capability to scan incoming traffic and block all suspicious connections. Furthermore, access control lists can be created to protect sensitive company data from getting into hands of the unauthorized people.
Call us now for the best Fortinet business firewall solution in Kenya.



