Sophos Firewall Distributor in Kenya
The world has indeed become a global village. What with companies having branches spread all over. As Sophos Firewall distributor in Kenya, the solution has been the most trusted solution for web application security and endpoint protection. Bringing together employees from different locations to collaborate on a project made possible without traveling. Company resources have been made available for access anytime from any location. This has been a requirement for mobilizing the employees working together but from different time zones. This arrangement brings to the fore the need to manage applications and device security. Sophos firewall offers are an all-inclusive security solution.
ORACO Kenya is a certified Sophos installer in Kenya. Below, we discuss the essential Sophos security features:
Why your company needs network firewall in Kenya
Sophos appliance enables institutions and businesses to manage centrally all active devices spread across branch offices. The central administration console gives the network administrator an easy time administering network resources.
With a centralized administration, updating network policies and even renewing licenses takes only a few minutes. Network engineers find it easy to support network devices such as routers and network switches. This is because of the device classification into easily identifiable groups.
In a centralized console, the IT support team creates usage policies and passes them on to other networks within the intranet.
On top of that, IT Support team does not need to keep a diary of subscription dates. The appliance has an inbuilt alert system for notifying the administrator of the due date for license renewal. Also, notification happens in case of a security breach or when a VPN connection drops.
An intelligent reporting and event logging system
The reporting system enables institutions to view network activities in real-time. The logs captured about user activities help in the creation of network security policies.
The over 800 comprehensive reports from Sophos firewall appliance identify security gaps that exist in the intranet. These reports help to enhance network security management through regular security audits.
See also; IP PBX phone system.
Real-time reports are accessible from the dashboard. From the dashboard, the IT support specialist narrows down to specific incidences. It is possible to focus on individual computers through MAC address binding. For instance, the technical support team can establish the exact computer sending or receiving spam emails. The system administrators use the reports to control the widespread distribution of malware across the network.
Network Security
Sophos security brings together several security features on a single device. Thus, the appliance offers an all-inclusive network security service. Cyberoam can be configured to work at the network gateway level. In so doing, the firewall shields networks against web application risks and high-level attacks.
This technology enables companies to distinctively pick out network users and manage their control behavior over the network. An efficient method for managing users can facilitate policy rollout for groups of users or categories. Security breaches in the network can not only be captured by the IP address but also through user login details. With layer 8 technology, it is easier to implement data security measures and ensure compliance with company policy.
Web and application security
Even though the web has a lot of useful information, it can be a dangerous place if unmanaged. Sophos web firewall offers protection against attacks from web applications. To start with, companies are known to limit their staff from accessing social websites. Regrettably, unchecked access to social websites such as Facebook, Instagram, and Twitter might affect employee productivity. As a result, Sophos enables network administrators in controlling access to these social websites. System administrators can group network users based on their job activities. For example, online marketers will be allowed to access Twitter and Facebook longer than employees from the finance department.
see; best call center system in Kenya
As a matter of fact, Sophos firewall in Kenya works very well at institutions of learning. In any case, students will be blocked from accessing websites with radical content. However, the same procedure applies. The system administrator only has to create an account with policies that have features specific to students’ needs.
Spam Email protection system
A slow network is an obvious characteristic of spam. Arguably, controlling spam emails from flooding an intranet is usually not an easy task. Incidentally, Sophos spam protection solution makes it easy to identify spam emails before they bring the entire network down.
see; Structured cabling and networking company
One of the consequences of spamming from a private network is the blacklisting of the network’s public IP. Ultimately, rapidly detecting and isolating end-user computers suspected of spamming the network saves a lot of damage. Even so, computers infected with malware are the major suspects when it comes to spamming the network. Therefore, it is advisable to ensure web and internet security is up to the right standards. To begin with, installing genuine antivirus software and keeping it updated has proved very useful in spam management.
Above all, as an authorized Sophos firewall distributor in Kenya, we believe in empowering users through training. We train the IT Support specialists to configure and administer the Sophos firewall. Presently, we are the only IT Support company with more than four Sophos Certified Network Professionals. Contact us now for this exciting deal. Buy your Sophos appliance from a reliable Sophos firewall distributor and get free training and support.
Affordable network security solution in Kenya
The Sophos XGS 2100 is an enterprise firewall ideal for big companies in Kenya with hundreds of users. Built with an Xstream architecture, it offers excellent performance. Moreover, it uses security heartbeat technology to offer real-time insight into user activities and application behavior in a corporate network. As a matter of fact, the entire IT infrastructure has been made visible to IT security analysts in totality. This kind of visibility has foiled many cyber attacks. And by using the Sophos firewall security heartbeat, the system responds automatically to detected malware and cleans it leaving a report of an incident cycle.
see; biometric access control system
The report comes in the form of a root cause analysis report showing how the threat entered the network, the computer attacks, and the applications affected. After that, a report of incidence response and threat mitigation is delivered to be used as a case study essential for protecting the network from future attacks. In short, Synchronized security works efficiently by delivering insights into the specific behavioral analysis of machines and the applications in question.
Get a better return on investment
The network firewall and the endpoint protection software working together brings about a better return on investment to the organization. Instead of each computer security system working in isolation, synchronization brings about collaboration. Convergence created when firewall shares security updates with endpoint protection actually boost entire network security.
Sophos Firewall Price in Kenya
| Price | KES 498,800 |
| Sophos appliance | XGS series |
| Subscription | THREE Years |
| License type | Advanced protection for both web and network security |
| Number of users | 100 |
| Setup, Configurations and Training | YES |
| Support | YES |
The value gained while the endpoint protection and network firewall are working is far much greater than what they offer when working independently. By choosing to automate the whole entire process, the IT security team is freed up to engage in other activities of high value to the company.

Handle complex malware attacks
Attacks from malware have increasingly become complex. Your ordinary endpoint security can longer offer zero-day protection. What is more, the basic firewall security feature found in a router can longer provide the needed protection against complex attacks such as ransomware attacks. As it is, complex malware can only be tamed by advanced threat detection systems.
see; time attendance system in Kenya
Reduce the attack surface area
The hackers have actually increased the areas of the target. The email system, the server computers, the endpoint devices. And even the IP PBX system was not spared either. All these services and devices running the services require individual monitoring. Investigating malware attack incidences on all of the computers requires a lot of time. Additionally, as the number of endpoints and servers increases, there will need to hire additional IT staff.
get better coordination of security strategy
There is a lack of coordination between endpoint security and network protection systems. Nonetheless, in a coordinated environment, endpoints share information with the firewall. No service can be safe unless all the exploits are closed. The hackers only need to exploit the vulnerabilities spotted in software in order to launch widespread attacks. This calls for synchronization of security platforms sharing of the latest intelligence, thwarting attacks before they happen.
Enhance internal capacity
A recent survey revealed that the IT industry actually faces a severe shortage of experienced cybersecurity specialists. The few who are available are in so high demand that hiring them becomes an expensive undertaking for small and medium-sized companies. Unfortunately, it is the small and medium-sized companies that are severely affected by cybersecurity-related incidences.
Increased visibility for the applications and the endpoints
The Sophos synchronized security brings all the devices and network services under one platform. Hence, all the details about the attacks are usually available. The IT security staff can view details about each device by simply clicking on the icon available on the dashboard. Furthermore, the health status of each device is highly visible so that the system administrator can choose the right action at any point in time.
Faster response to threats
With ordinary antivirus software, it might as long as two hours to isolate the affected computer, neutralize threats, and return the endpoint back to the network. Essentially, the endpoint protection software communicates to the central security system about a malware attack. The central security system conveys the information to other endpoint computers in the network warning them about the attack.
The firewall system isolates the affected endpoint from the network thus stopping the malware attack from spreading further. The infected endpoint computer is cleaned while still in isolation. Once the endpoint health status has been restored to normal, network access will be restored. All this process happens in seconds.
Synchronized Security
With the standard antivirus software, incidence response and threat mitigation sometimes took weeks in processing. Today, synchronized security has reduced human effort involvement during threat management to near zero. With automation, it takes less than 8 seconds in threat investigation, to the identification of affected machines, and isolation to narrowing down to the particular application.
see; best CCTV camera installer
Contact us today for Sophos synchronized security; seamless integration between endpoint protection and network firewall services. As Sophos firewall distributor in Kenya, contact us now for the best Sophos XGS 2100 price in Kenya
deep learning threat detection technology
Sophos Intercept X is a network security technology that combines deep learning, and threat detection and response to protect endpoints from cybersecurity threats such as ransomware. This is an advanced endpoint protection technology developed from machine learning methodologies to curb zero-day attacks. Thus, the Intercept X assures of intelligent and unmatched accuracy levels while providing endpoint protection. Even for the Sophos Firewall.
Sophos Intercept X is about the consolidation of protection services and enjoying the power of machine learning in threat detection and prevention. This system helps IT, security analysts, to understand the operating environment by presenting a simple to use reporting dashboard. This is because a better understanding of the scale of attacks and overall impact on the organization’s operations leads to better resource planning.
see also; SIP Trunk provider
Good planning leads to adequate preparedness in the event of an attack. Since the threats are detected early enough, they neutralized instantly and intelligence shared across the platform.

Ransomware and Malware protection
Sophos Intercept X uses CryptoGuard, which is an efficient ransomware protection technology based on artificial intelligence. Basically, it not only stops known threats but will also unknown attacks from propagating. This is made possible through behavior analysis technique; a machine learning methodology that flags threats based on behavioral hints.
Still, after removing corrupted files, Sophos will go a step ahead to remove all the forensics data associated with malware. Unlike the ordinary antivirus software that only does surface level removal of affected files and documents.
see also; best payroll software in Kenya
Exploit detection and prevention
Hackers have become very smart. They hardly leave a trail upon a successful attack. However, Sophos uses an exploit prevention technique to curb non-detection. Through this feature, hackers are blocked before even launching attacks. By the same token, Intercept X blocks the loophole being exploited to carry the attacks. Hence, Sophos curtails the distribution of malware inside the corporate network. Sophos Firewall distributor.
Synchronized protection
Beating hackers at their own game requires timely gathering and sharing of the latest intelligence about suspicious traffic, compromised email or corrupted files. The information-sharing happens between the network firewall and the endpoints. This leads to synchronized protection. Synchronized protection ensures that information threat is shared across the platform.
see also; intercom system installation
By sharing regular updates about detected threats, endpoints are protected from distributed network-wide attacks. More importantly, the network firewall gets to isolate the infected computer and until a manual action is completed. The manual action will ensure that the threat is completely neutralized.
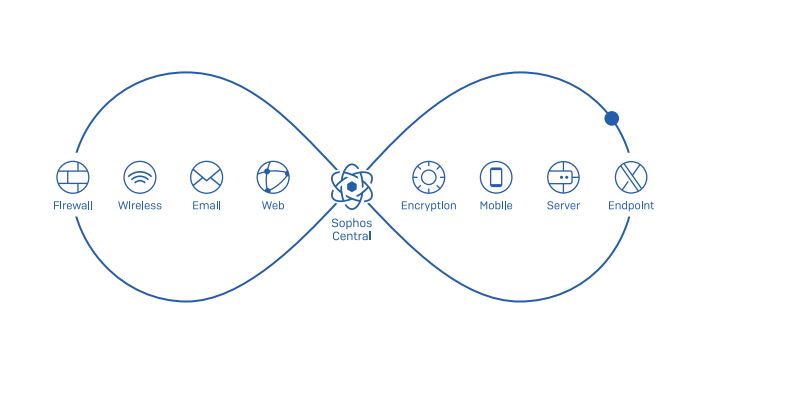
Consolidation of the network protection services
Sophos central brings together all the network protection services under a single management console. The dashboard gives one-click access to all protection services be it servers, mobile devices, endpoints, email services, and even wireless networks. Also, it is from the dashboard that a network security analyst will spot compromised files and devices.
see; automatic gate opener system
Furthermore, Sophos XGS 2100 comes with the ability to pinpoint a problem based on the specific device name or user account signed in with. For this reason, it enables faster action to be against the identified or potential breach. Above all, the Intercept X offers a huge plus through integration with the Sophos central. This enables a system security analyst to use the central console to manage different services.
Contact us today for IT systems audit, and network security solutions from the best Sophos firewall distributor in Kenya.



